WRITER: Jeremy Fuchs, Cybersecurity Researcher/Analyst at Check Point Software Company
Introduction
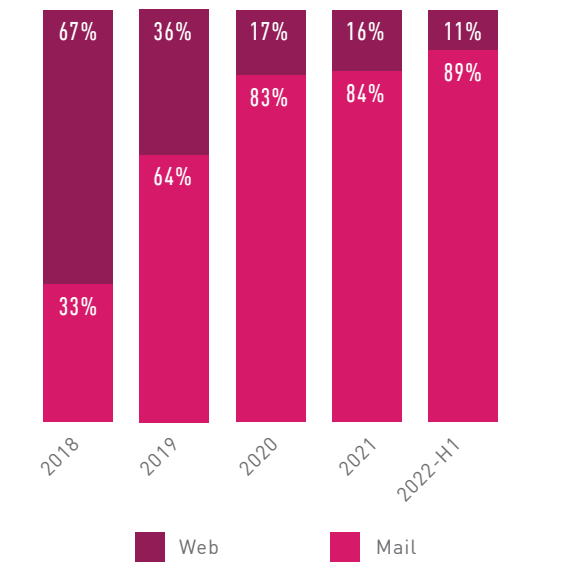
Email threats continue to increase. In the first half of 2022, according to Check Point Research, email-delivered attacks reached 89% of all in-the-wild attacks.
It’s increasingly become the hackers’ favorite method of entering an environment, including over web-based attacks:
This increase in hacking activity has led security solutions to try and find ways to improve their defenses. As security improves against different attacks, hackers have to adjust.
One attack type that has worked is brand impersonation, when a hacker makes an email look like it comes from a trusted brand.
As we’ve written extensively, hackers are ditching brand impersonation and going for the real thing.
The new way that hackers originate Business Email Compromise (BEC) 3.0 attacks is through legitimate services.
There is no need for tedious research or complex social engineering. Sign up for a free account at a popular, legitimate site and send a link directly from the service. These campaigns are soaring inboxes around the world.
In this Attack Brief, Check Point Harmony Email researchers will discuss how hackers create malicious documents within Dropbox, then send a legitimate link from Dropbox, with a file sharing to a fake OneDrive link.
Attack
In this attack, hackers create free Dropbox accounts and leverage their domain legitimacy to create pages with phishing embedded within them.
- Vector: Email
- Type: BEC 3.0
- Techniques: BEC, Social Engineering
- Target: Any end-user
Email Example
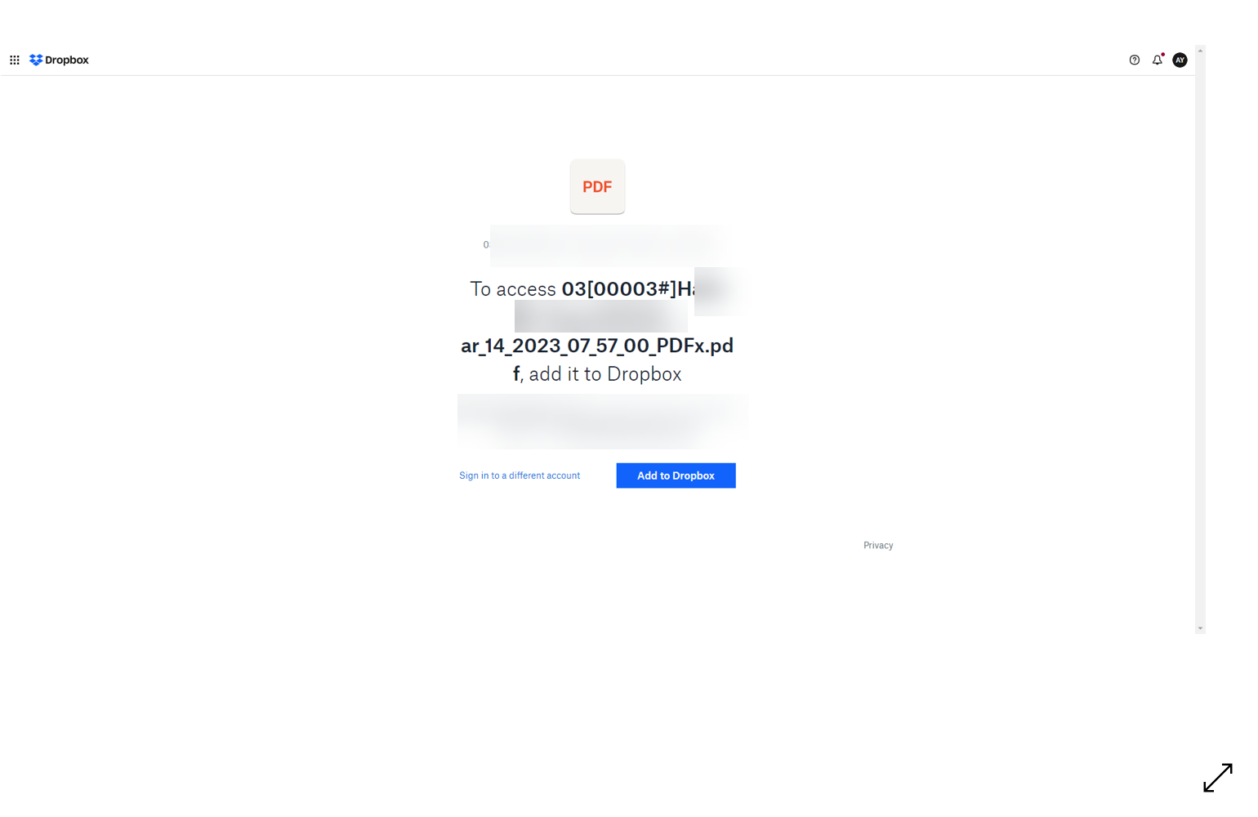
It starts with someone sharing a PDF of someone’s resume via Dropbox. To see it, the end-user must “Add to Dropbox.” The link initially came from Dropbox, meaning there’s nothing malicious about the first communication. Dropbox is a legitimate site, and there’s nothing wrong with it. How hackers are using it is a different story.
Step 1: Once they click and get into Dropbox, they will see this page hosted on Dropbox. Users must enter their email account and password to view the document. Now, even if users go beyond this step, hackers have their email addresses and passwords.

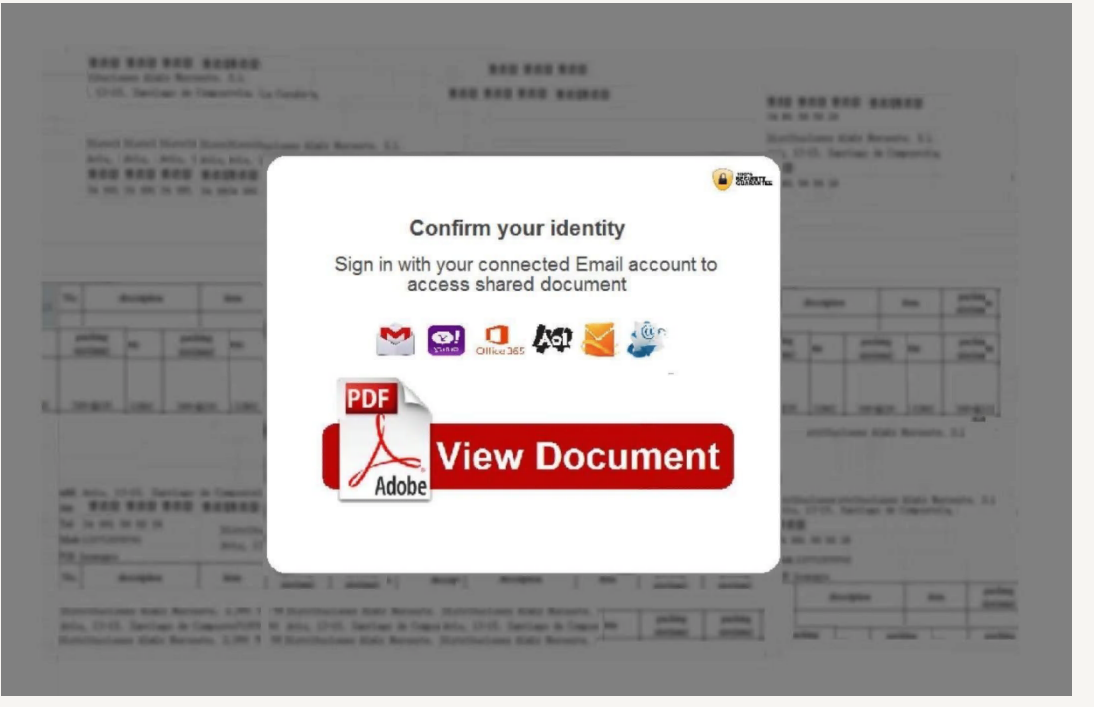
Step 2: Once users enter their credentials, they will be directed to this site, which leads to a malicious URL.
So, the hackers, using a legitimate site, have created two potential breaches: They will get your credentials and then potentially induce you to click on a malicious URL.
That’s because the URL itself is legitimate. It’s the content on the website that’s problematic. You’ll see the hackers mocked up a page that looks like OneDrive. When clicking on the link, users are given a malicious download.
Techniques
Hackers are nothing if not clever. They will work on an attack until security services or end-users find a way to stop or ignore it.
We’ve seen hackers do a lot of BEC attacks. These attacks have several variations, but generally, they try to spoof an executive or partner to get an end-user to do something they don’t want to do (like pay an invoice to the wrong place).
We’re now seeing an uptick in BEC 3.0, where legitimate services are leveraged to send phishing content directly: the next evolution of difficult and damaging attacks.
Leveraging legitimate websites to host malicious content is a surefire way to get into the inbox.
Most security services will look at the sender–in this case, Dropbox–and see that it’s legitimate and accept the message. That’s because it is legitimate.
This attack type requires a few things. It starts with complete suite protection. Though this attack is first started via email, it morphs into a file-sharing concern when it hits Dropbox. Scanning for malicious files in Dropbox–and emulating links in documents–is critical. That includes replacing links in the email body and inside attachments, ensuring that Phishing attacks that utilize attachments with links are also prevented. This protection must extend every time a user clicks on that link.
Another big thing is education. But how do you educate users on legitimate links? A big thing is context. Look at the example above. Think about how it applies to your organization. Are resumes typically sent via Dropbox? If not, it may be a reason to contact the original sender and double-check. If they are, take it one step further. When you log into Dropbox, do I have to log in again with my email?
Taking just a few seconds to consider what the sender wants you to do can spare you considerable trouble.
Check Point Harmony Email researchers reached out to Dropbox on May 15h via their report phishing feature to inform them of this attack and research.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement security that looks at all URLs and emulates the page behind it
- Educate users on this new variant of BEC
Leverage AI-based, anti-phishing software capable of blocking phishing content across the entirety of the productivity suite.