Kaspersky unveiled a malicious campaign in which an installer of the Free Download Manager software was employed to disseminate a Linux backdoor for a minimum of three years.
Researchers discovered that victims were infected when they downloaded the software from the official website, indicating that this is a possible supply chain attack.
Variants of the malware used in this campaign were first identified in 2013. Victims are based in various countries, including Brazil, China, Saudi Arabia, and Russia.
Kaspersky experts identified a new malicious campaign targeting Linux systems, where threat actors deployed a backdoor – a type of Trojan – onto victims’ devices using infected version of a popular free software: Free Download Manager.
Once the device is infected, the attackers’ goal is to steal information such as details about system, browsing history, saved passwords, cryptocurrency wallet files, and even credentials for cloud services like Amazon Web Services or Google Cloud.
According to Kaspersky’s telemetry, victims of this campaign are located all over the world, including Brazil, China, Saudi Arabia and Russia.
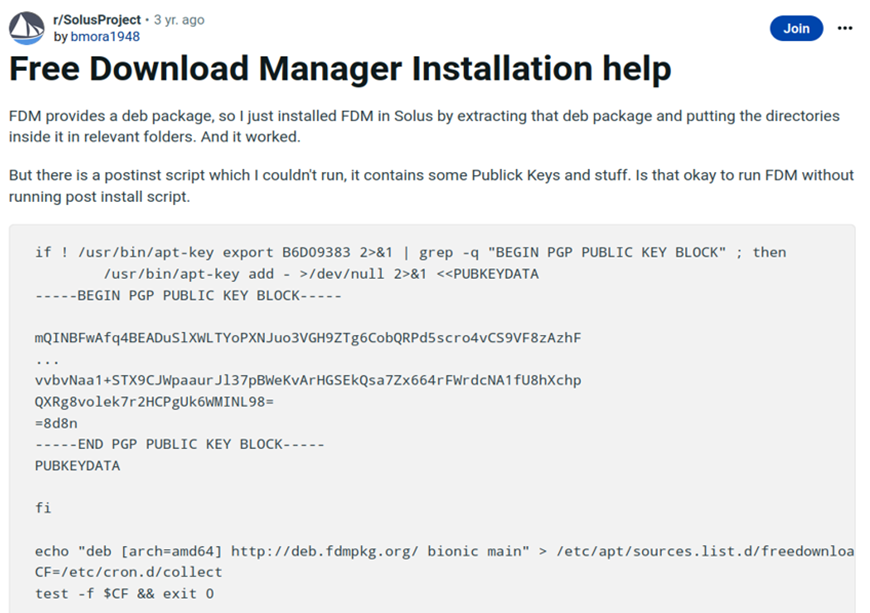
Kaspersky experts believe it is likely that this is a supply chain attack. During the investigation into Free Download Manager installation guides on YouTube for Linux computers, the company’s experts found instances where video creators inadvertently showcased the initial infection process: clicking the download button on the official website resulted in a malicious version of Free Download Manager being downloaded. In contrast, in another video, a legitimate version of the software was downloaded.
It is possible that the malware developers scripted the malicious redirection to appear with some degree of probability or based on digital fingerprint of the potential victim. As a result, some users encountered a malicious package, while others obtained a clean one.
According to Kaspersky’s findings, the campaign lasted for at least three years – from 2020 to 2022. The malicious package installed the Free Download Manager version released in 2020.
Moreover, over the course of this timeframe, there were discussions on websites such as StackOverflow and Reddit about problems caused by the infected software distribution. However, the users were unaware that these issues were caused by malicious activity.
“Variants of the analysed backdoor have been detectable by Kaspersky solutions for Linux since 2013. However, there is a widespread misconception that Linux is immune to malware, leaving many of these systems without adequate cybersecurity protection. This lack of protection makes these systems attractive targets for cybercriminals. Essentially, the Free Download Manager case highlights the challenge of spotting an ongoing cyberattack on a Linux system with the naked eye. Therefore, it’s essential for Linux-based computers, including both desktops and servers, to implement reliable and effective security measures”, says Georgy Kucherin, a security expert at GReAT, Kaspersky.
To avoid Linux-based and other types of threats, it is worth implementing the following security measures:
- Choose a proven endpoint security solution such as Kaspersky Endpoint Security for Business that is equipped with behaviour-based detection and anomaly control capabilities for effective protection against known and unknown threats.
- Use Kaspersky Embedded Systems Security This adaptable, multi-layered solution provides optimised security for embedded Linux-based systems, devices and scenarios, in compliance with the rigorous regulatory standards so often applicable to these systems.
- Since the stolen credentials may be put up for sale on the dark web, use Kaspersky Digital Footprint Intelligence to monitor shadow resources and promptly identify related threats.