Writer: JEREMY FUCHS, Cybersecurity Researcher/Analyst at Check Point Software
The hottest trend in the phishing world is leveraging legitimate services to send illegitimate messages. It’s easy for hackers—sign up for an account, often free, at a variety of websites. We’ve seen things like Microsoft, Google, QuickBooks and PayPal.
From the services in the tool, send out an email—an invoice, a document. The email comes directly from the service and is sent into the inbox, passing all typical checks.
It’s easy for hackers to do, hard for security services to spot and difficult for end-users to notice.
A winning trifecta. Now, we’re seeing yet another legitimate tool used for these purposes—AWS.
In this attack brief, Check Point Harmony Email researchers will discuss how hackers are using AWS to send out phishing links.
Attack
In this attack, hackers are utilizing sites hosted on AWS S3 Buckets to send phishing links.
- Vector: Email
- Type: BEC 3.0
- Techniques: Social Engineering, Credential Harvesting
- Target: Any end-user
Email Example
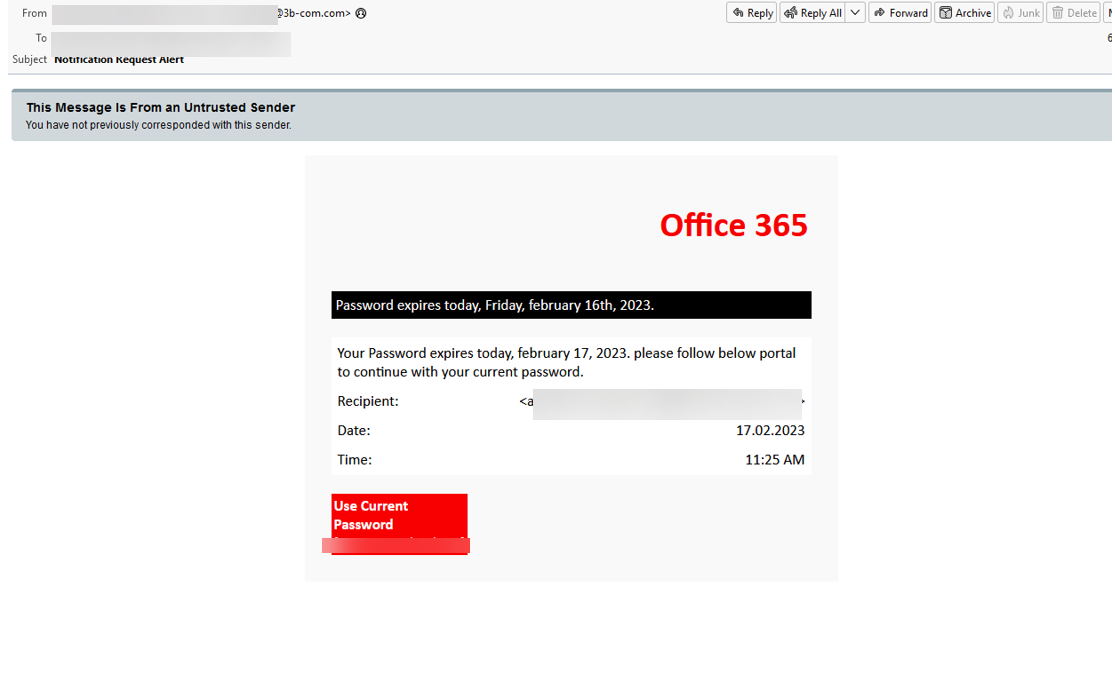
This starts with a standard-looking phishing email, requesting a password re-set. For many users, this email may be enough to stop engaging. Security services may be able to pick up on it, given the discrepancy in sender address. But the link in the address goes to an AWS S3 bucket, which is legitimate.
Should the user click on the link, they will be re-directed to the following page.
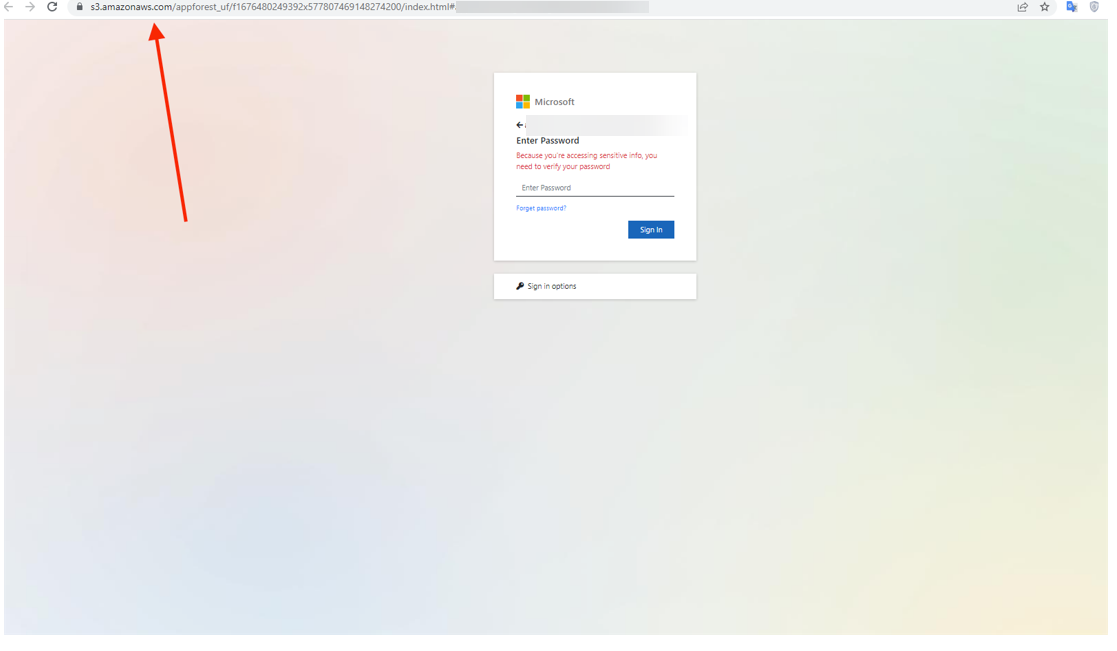
There’s a few things to notice. First is the URL. It’s an S3 Bucket, a legitimate AWS site. Anyone can host a website—static or dynamic—on AWS. It requires a little more coding skills than some of the other BEC 3.0 attacks, but it’s not a huge lift.
Second, the hackers re-create a Microsoft login page. Further, the email address is already populated—user just has to enter the password. You’ll also notice in the URL bar that there’s a blurred out part. That’s where the email address of the victim goes, making it look like they are already logged in.
Techniques
Unlike some of the BEC 3.0 attacks we’ve been chronicling, this attack requires slightly more technical skills on behalf of the attacker. That said, it’s still basic enough for the average hacker to execute.
The attackers are aiming for credentials. Once you get the credentials, you’ve got the keys to the kingdom. In this attack, the attackers are using an S3 bucket to host a webpage that will re-direct the credentials back to them.
It’s fairly convincing—although not, as we’ll admit, as convincing as some of the others we’ve talked about recently on our blog.
Still, it follows a practice that most users are familiar with—the banal task of resetting a password. It provides a look-a-like Microsoft login page. And the email is already populated, a nifty trick by hackers to lend legitimacy.
End-users can spot this attack by looking at the URL. But we know that that’s not always the case. It’s far easier to just enter your password and get the reset over with.
That’s what hackers are hoping for.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement security that uses AI to look at multiple indicators of phishing
- Implement full-suite security that can also scan documents and file
- Implement robust URL protection that scans and emulates webpages









Comments 1