-
Phishes roasting in an open email…malware nipping at your nose. It’s Phishmas and all the hackers are stirring–even your mouse!
-
It’s that most wonderful time of the year–Phishmas, when hackers get out their naughty and nice list and check it twice. It’s the holiday season when hackers are hard at work trying to phish as much as possible.
-
In fact, according to Check Point, 17% of all malicious files distributed by email in November were related to orders and shipping; one scam involving a fake Louis Vuitton domain saw 15,000 attacks in a week.
Check Point Software Technologies Ltd., a leading provider of cybersecurity solutions globally, believes that in December, this will reach a crescendo. We’ve taken a number of different attacks that are circulating this holiday season and put them together so you can see the potential impact these can have.
These attacks tend to take advantage of shipping and package notifications, as you can imagine, but they go beyond that. We’ve seen a noted increase in impersonation and payment fraud.
You need money to pay for holiday gifts, and impersonating payment notifications or direct deposit can be a great way to scam someone out of money.
Just remember, when it comes to the holidays and email security, it’s much easier to prevent presents from being bought as opposed to taking them away after they’ve been placed under the tree.
Direct Deposit Scam
In order to buy presents, you need money. In that vein, we’re seeing an influx of phishing campaigns surrounding Direct Deposit.
The general idea is that a scammer will pose as an employee asking HR or a manager to change their direct deposit information.
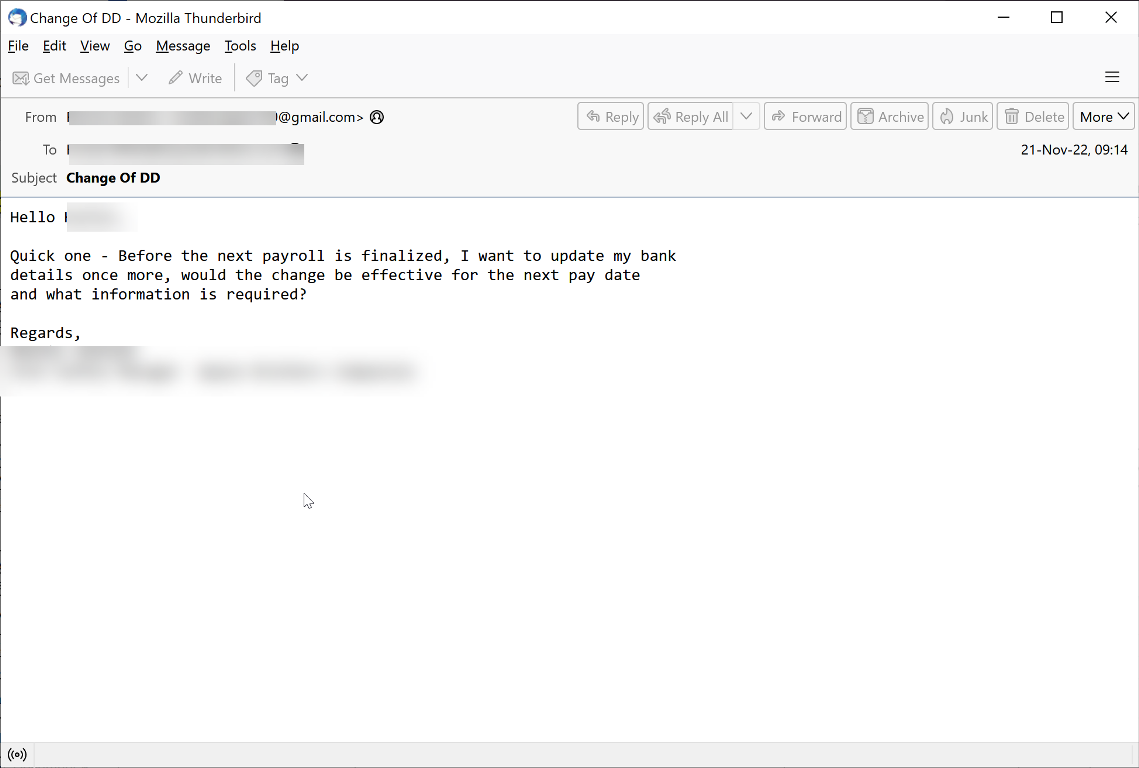
In this email, a scammer is impersonating an employee. However, the sender address is a Gmail account. The person asks to change their direct deposit information. Of course, if the change is made, payments will go to the scammer, not the employee.
And if that’s the case, it will make for a bleak holiday for the company and employees alike.
Though this happens all the time, the fact that we’re seeing an influx around the holiday is an interesting trend. It means that hackers are actively targeting people when they are likely to spend their money the most. Here’s the latest example:
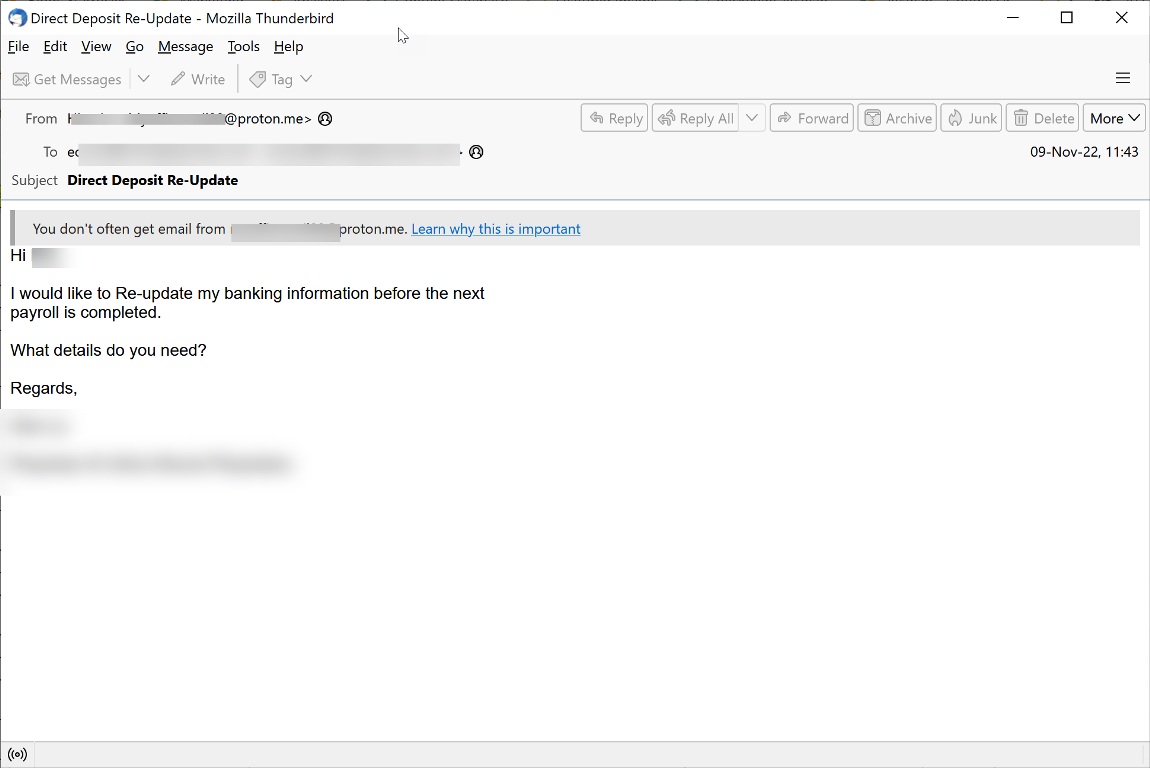
You’ll notice that the email comes from a “proton.me” address, and not the company’s address. That’s a tell-tale sign that something is amiss.
In this case, the formula remains the same. Ask for HR to change direct deposit details. Money gets diverted elsewhere.
Direct Deposit scams are common. In fact, here’s another example we have found:
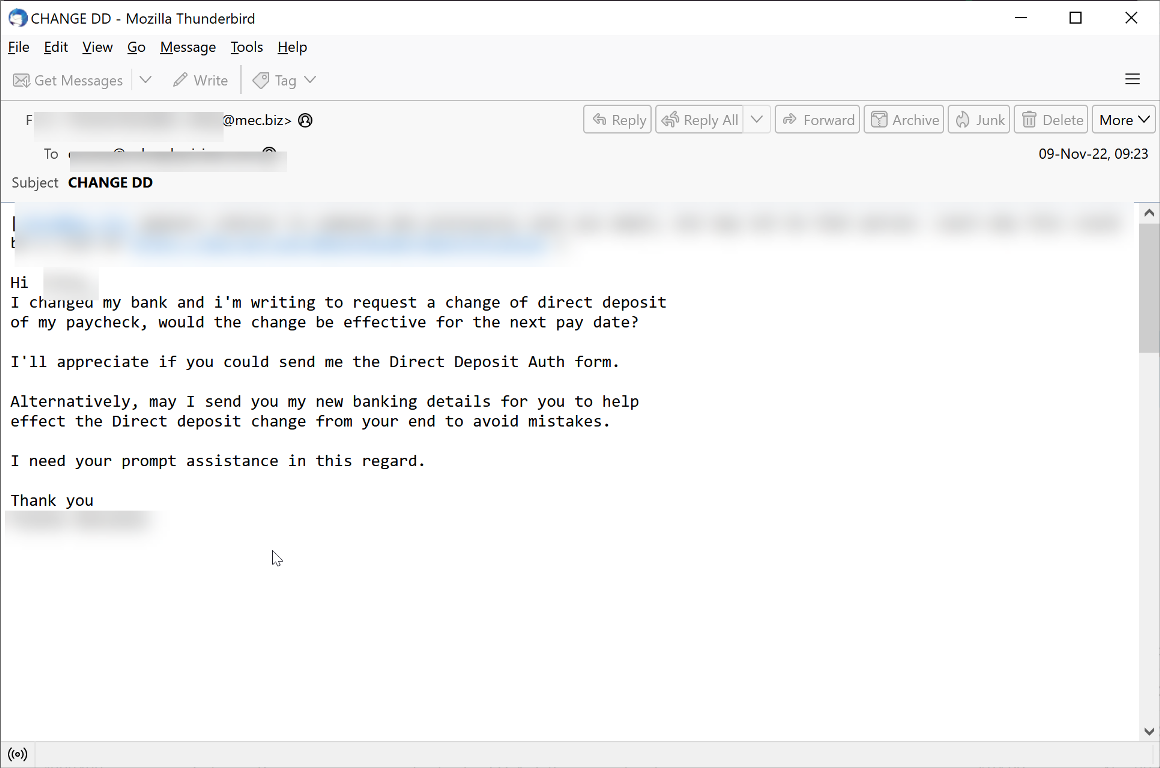
These scams are not super sophisticated. What makes them tricky, however, is the lack of malicious link or attachment. Security scanners often look for those items, since if it’s malicious, it’s an easy block.
When it’s just text, it becomes a bit harder. It’s not entirely out of the ordinary for an employee to change their bank account information. People change banks; sometimes they want their money deposited into multiple accounts. This email in and of itself is not malicious.
The text, however, is where the danger lies. A good email security solution would see that the sender address doesn’t match the company address and block it accordingly
The Verification Email
During Phishmas, you can expect a large increase of phishing emails from shipping companies like UPS, DHL, and FedEx. End-users receive tons of legitimate emails from these companies, making these scam emails seem more legitimate.
In this email, we see a spoof of UPS. The scammers are asking for the user to confirm their email address.
That link, however, goes to a credential harvesting page.
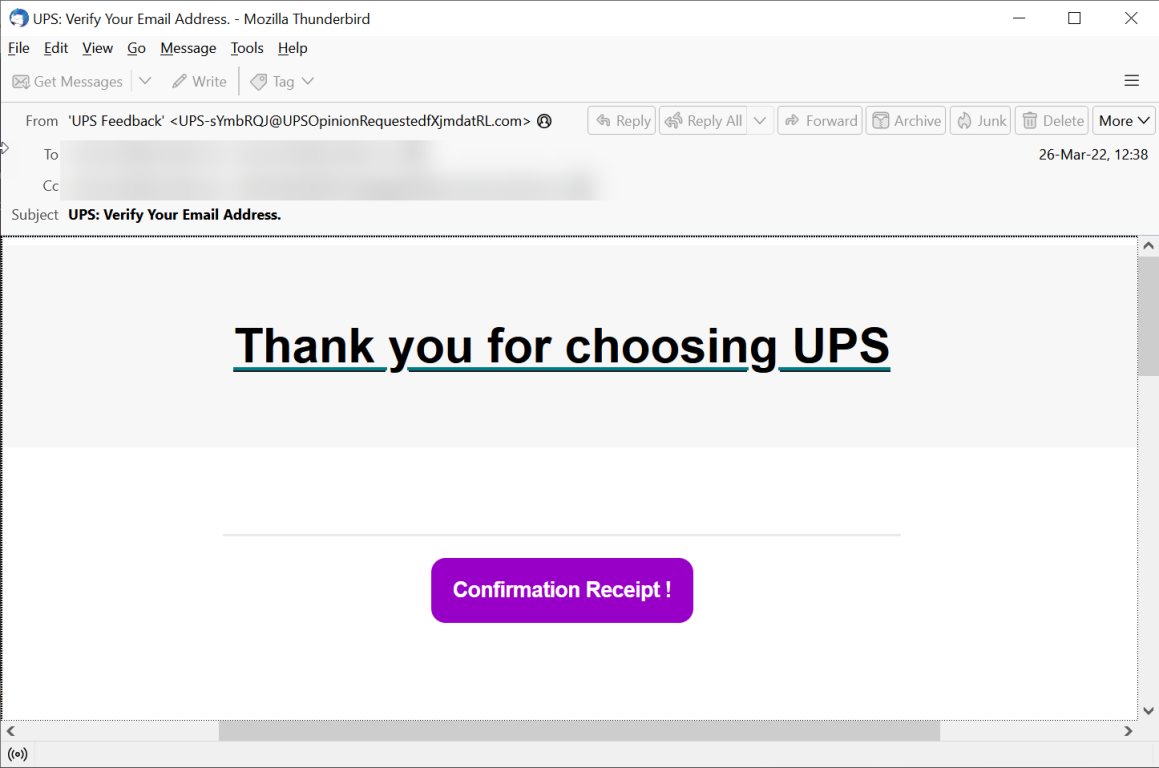
Notice that the sender address is not actually from UPS. This holiday season, check sender addresses before responding to anything–and be sure to check it twice to see who is naughty or nice.
USPS Delivery Status
Of course, we also expect to check delivery companies for package and delivery status.
Hackers know this and will use it to phish their victims. This example is no different. In here, the email comes from the salesperson at the store, trying to be helpful. The salesperson is saying that the USPS wasn’t delivered and attaches an email that claims to come from USPS.
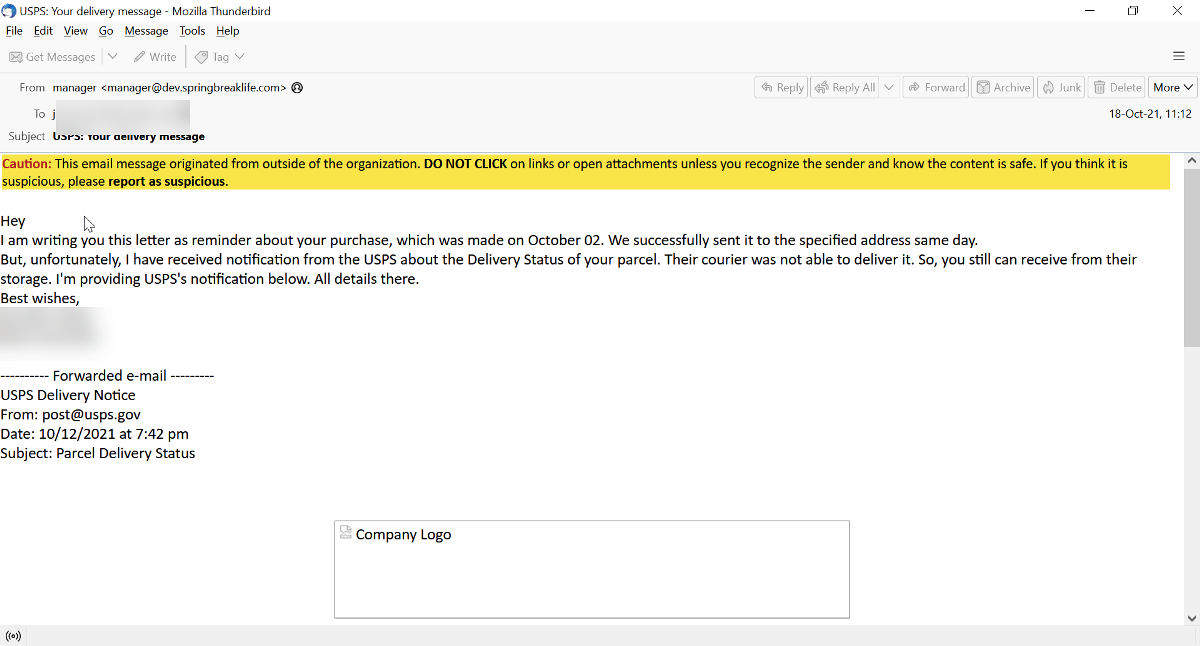
This is part two of the email.
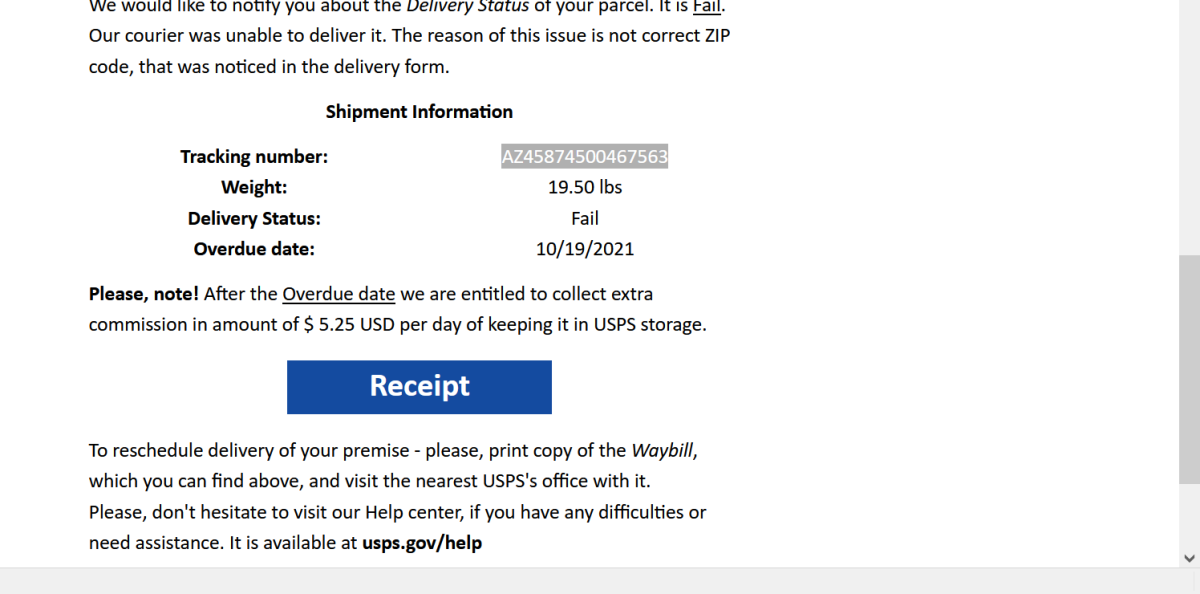
The link to “Receipt” goes to a OneDrive page, meaning the malicious content is hosted via the file-sharing platform. This is another example of The Static Expressway.
There’s also a call to urgency, with an “overdue date” that will cost the recipient $5.25 a day in storage.
Further, notice how they say you can ask for help at USPS.gov. Note that the official USPS URL is USPS.com
When getting shipping emails this Phishmas season, it’s important to pay attention to:
- The Sender Address
- The Grammar
- The Logic
What do we mean by logic? Many phishing emails don’t follow standard logic. For instance, paying to verify your address. Or saying, “Dear Email User”. When evaluating an email, if the logic isn’t there, it’s probably not safe.
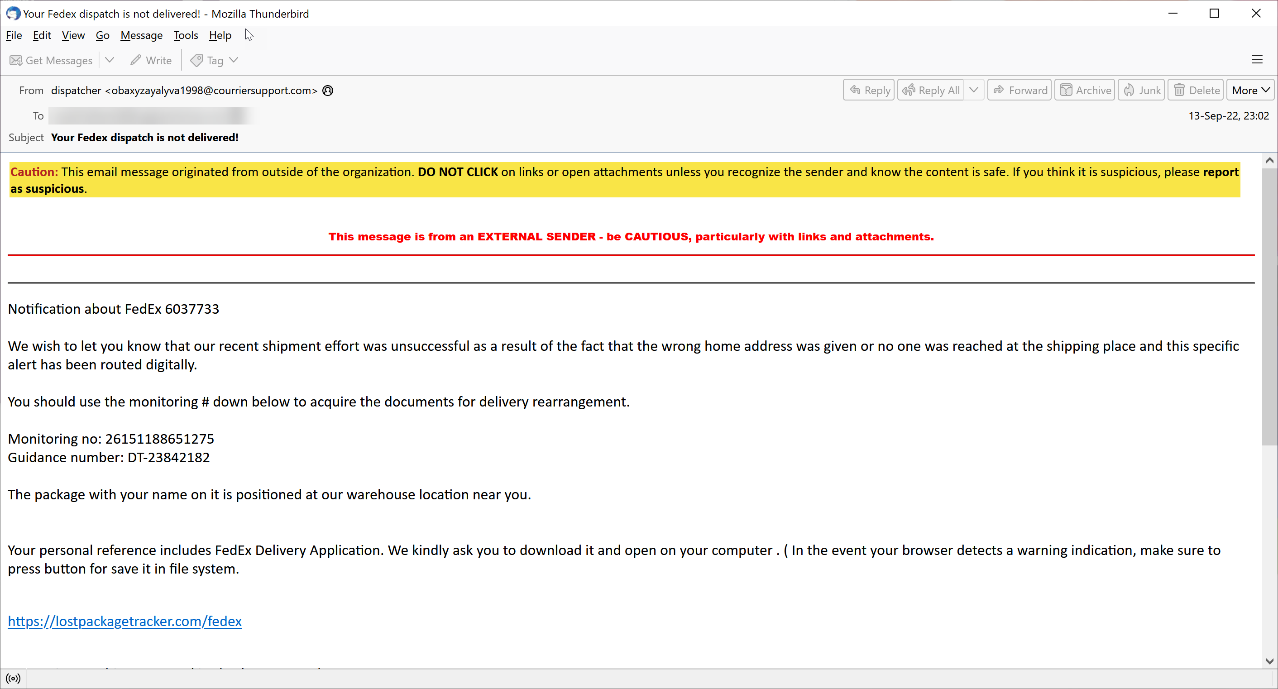
The FedEx Sender Spoof
You must make sure you know how to spot all the signs of a bad email.
This email claims to come from a Fedex.com address–although in this case, it’s a clear spoof of the domain.
That’s the only thing that ties to shipping. Everything else is a really poor spoof of a McAfee subscription. There are spelling errors everywhere–it would be a good idea to spell McAfee right in the spoof.
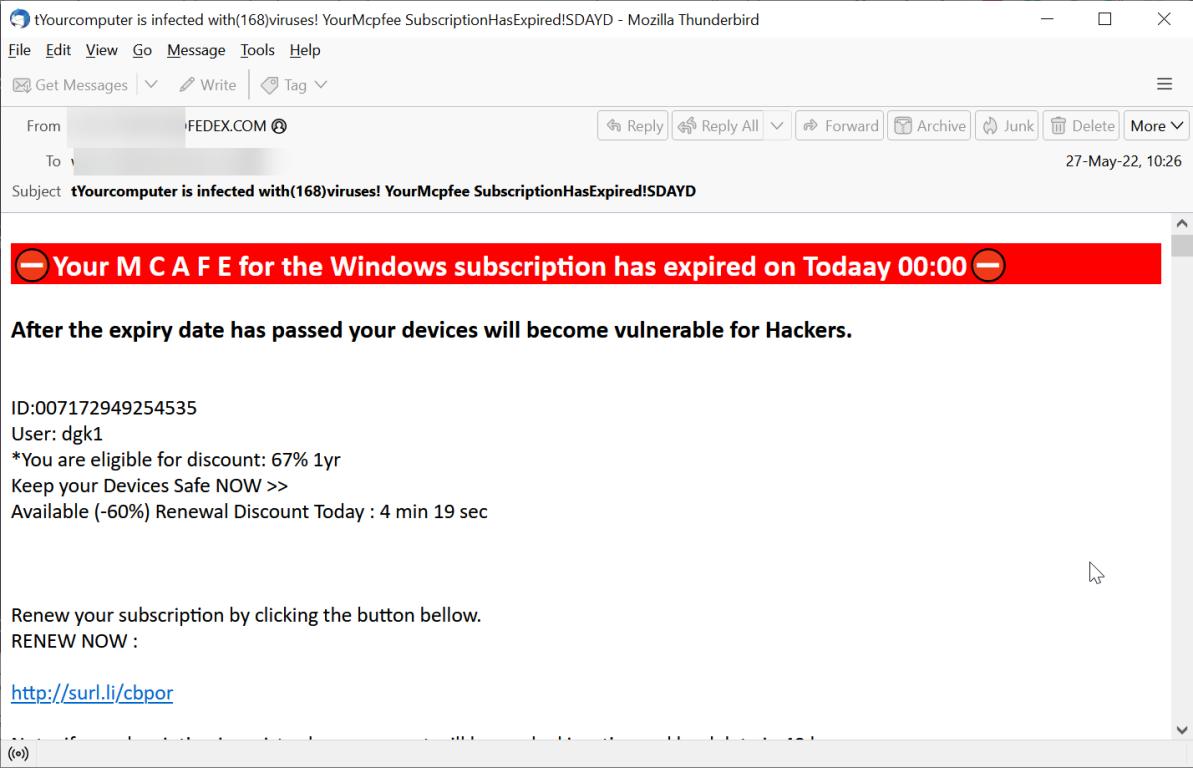
The URL is a clear credential harvesting scheme.
When you see an email like this, even if the sender address appears legitimate, look at the rest of the email. That will alert you that the sender address is actually a spoof.
Is Your Address Correct?
We’ve all gotten some variant of this email before, even legitimate ones. A package can’t be delivered. Maybe they couldn’t get access to a building; maybe the address was typed incorrectly.
This attack, which does a fairly good job of spoofing FedEx, claims that FedEx couldn’t deliver your package, because the delivery address was wrong.
In order to remedy this, they want you to fill in some information on an attachment. This attachment is actually fairly common, and it is indeed malicious.
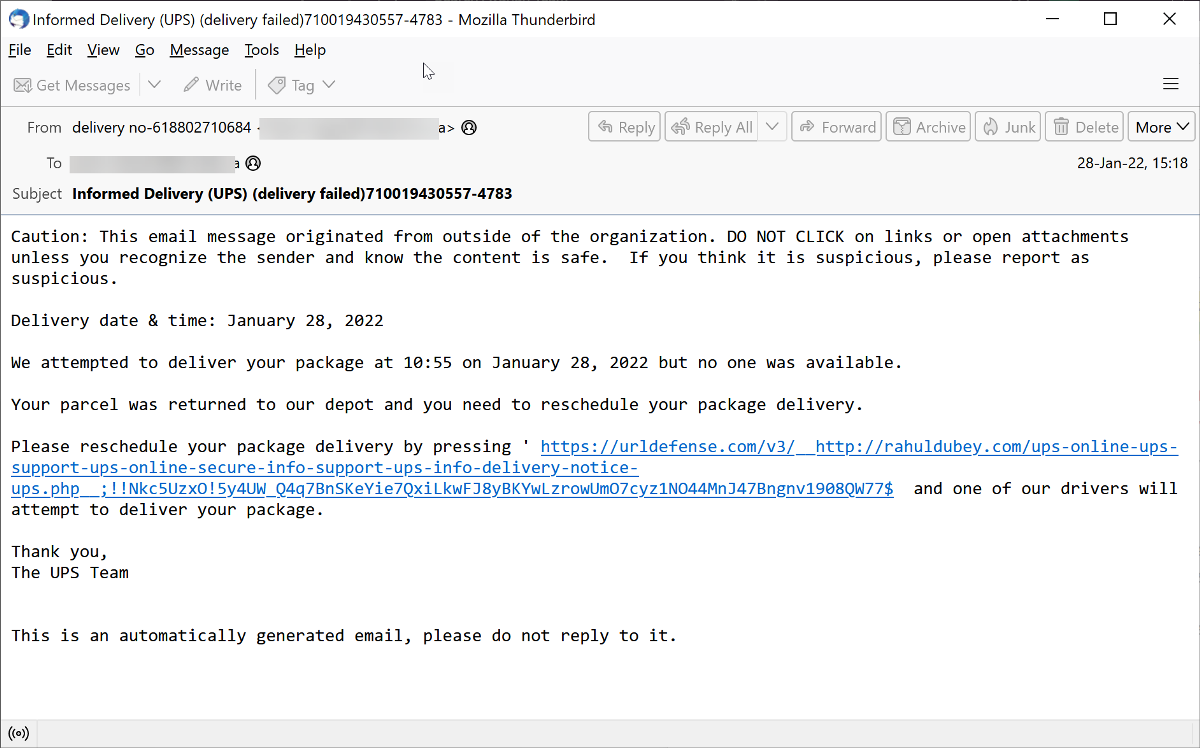
The Failed Delivery
There are few things more frustrating than getting a notification that a package couldn’t be delivered. It requires far too much work to get it back on track. But when you have a package that needs to be delivered, you’ll do what it takes. That’s what this phishing scam aims to take advantage of.
In this email, the URL at the bottom links to a downloadable component. The email kindly asks you to download it, and to ignore any warnings that it may be dangerous. That should be the ultimate signal something is off.
Summary
This Phishmas, be on the lookout for a tremendous number of attacks. Hackers want to be the Grinch and steal your holiday cheer. But if you look at an email properly, you can stay safe. Here are some things to pay attention to:
- Sender Address
- URL
- Logic
And if unsure, always check your account on your online shopping store or courier company by directly typing in the URL into the address bar.