Telegram entered 2026 under unprecedented pressure, executing its most aggressive crackdown to date.
Millions of channels and groups were removed, enforcement automation was scaled up, and transparency around moderation reached an all-time high.
Yet, the very communities targeted, cybercriminal networks which thrive on the platform, have proven remarkably resilient.
Rather than disappearing, these illicit ecosystems are reorganising, evolving, and staying one step ahead, underscoring a growing paradox: Telegram’s enforcement is record-breaking, but the threat landscape is not shrinking.
The implications for Nigeria’s estimated eight million users are sobering. According to research published by Statista, Nigeria has the largest Telegram user base aged between 16 and 64 in Africa.
The platform is widely used for trading – particularly cryptocurrency and mining, as well as online betting and gambling.

“Rather than disappearing, these illicit ecosystems are reorganising, evolving, and staying one step ahead, underscoring a growing paradox: Telegram’s enforcement is record-breaking, but the threat landscape is not shrinking,” says Kingsley Oseghale, country manager: West Africa, Check Point Software Technologies.
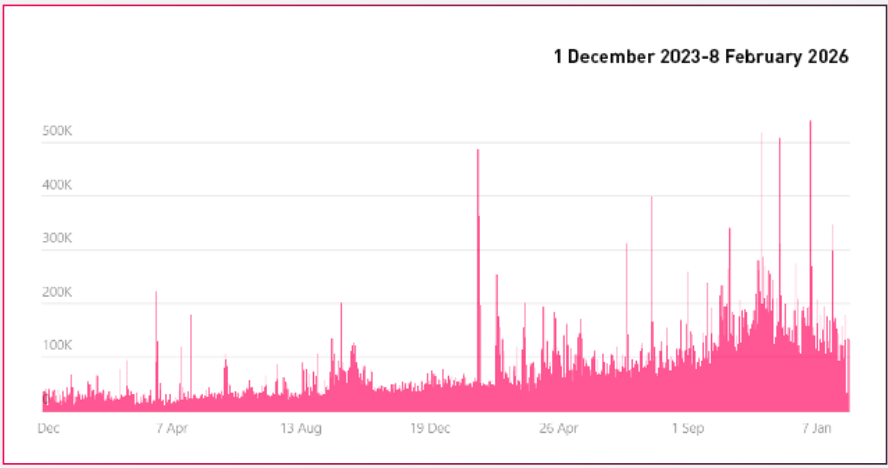
Telegram’s enforcement numbers are staggering. In 2025 alone, more than 43.5 million channels and groups were blocked, and daily takedowns have surged from roughly 10,000 to 140,000, with peaks exceeding 500,000 in a single day.
Yet even at this unprecedented scale, the platform’s crackdown has not dented the presence of cybercriminal communities.
Record-Breaking Moderation Has Not Reduced Criminal Presence
Telegram’s enforcement activity shows the sheer scale of the crackdown. Moderation is accelerating into 2026, but the persistence of illicit communities highlights the limits of even the most aggressive takedown strategy.
Based on new intelligence from Check Point Exposure Management, here are three of the latest developments in the realm of Telegram following Telegram’s crackdown in 2026.
Despite daily takedowns surging to 140,000, with peaks exceeding 500,000 in a single day, even at this unprecedented scale, the platform’s crackdown has not made a dent on cybercriminal communities.
Instead, these networks continue to adapt, reorganising faster than they are removed and finding new ways to exploit Telegram’s reach, speed, and anonymity.
On the surface, this suggests unprecedented progress. In practice, the impact is more nuanced.
Check Point Exposure Management analysis shows that roughly 20 percent of blocked channels were linked to criminal activity that directly affects businesses, including carding operations, Fullz trading, and hacking services.
Thousands of messages referencing blocked channels continue to circulate, especially via forwarded content that keeps criminal knowledge alive even after takedowns.
The key issue is persistence. Channels disappear, but communities reform quickly. Backups are pre-created for many of the channels that are taken down, often even before the takedown happens, so that the community is ready.
In fact, often, the audiences are preloaded, and operational continuity remains largely intact. Enforcement has increased friction, but it has not eradicated the use of Telegram by cyber criminals.
Threat Actors Are Adapting Faster Than Platforms Can React
Rather than leaving Telegram, threat actors have evolved how they operate inside it.
Several evasion techniques now appear consistently across underground communities. Many groups use “Request to Join” gating to block automated moderation bots.
Others add disclaimers in channel bios, tagging Telegram leadership and claiming compliance even when engaging in illicit activity.
Backup channels are created in advance, sometimes bundled together, allowing instant reconstitution after a takedown.
Check Point data shows spikes in forwarded messages referencing blocked sources, especially during peak enforcement periods in February, March, and April 2025. Criminal content continues to circulate even when original sources are removed, extending the lifecycle of fraud data and operational guidance.
This adaptation mirrors broader trends in cyber crime. Attackers no longer rely on a single asset or channel. They assume disruption and engineer redundancy. Telegram’s scale, usability, and discoverability still make it uniquely attractive for this approach.
Understanding these behavioral patterns is critical for proactive defense. The ebook dives deeper into how these evasion methods are evolving and why they matter for enterprise security teams.
Telegram Remains the Dominant Criminal Communication Hub
If moderation were truly displacing criminal communities, migration would be obvious. It is not.
Despite brief experimentation with alternatives, Telegram remains the platform of choice. Over the last three months alone, Check Point Exposure Management identified approximately 3 million Telegram invite links shared across underground environments.
By comparison, Discord accounted for fewer than 6 percent of that volume, while Signal, SimpleX, and Matrix-based platforms barely registered.
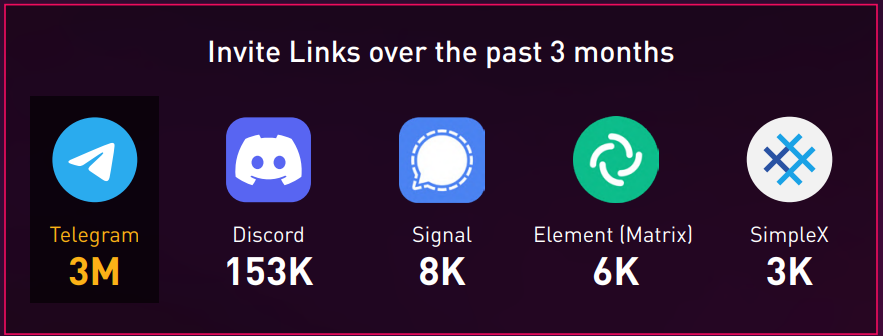
Even high-profile attempts to move failed. One notable threat group, AKULA temporarily relocated to SimpleX in early 2025 but returned to Telegram after followers did not migrate at scale. Some actors now use alternative apps for one-to-one communication, but Telegram continues to serve as the primary broadcast, recruitment, and marketplace layer.
Network effects matter. Telegram’s massive user base of more than 800 million active users makes it difficult for competitors to replicate its reach. Enforcement has changed behavior, not allegiance.
For SOC teams, this means Telegram remains a critical environment for exposure management, brand protection, and early threat detection. Ignoring it creates blind spots attackers will exploit.
Is Telegram’s Crackdown Actually Real?
“Telegram’s crackdown is indeed real, sustained, and growing. But so is the adaptability of cyber criminals. Although takedowns are still key, discovering the cyber criminal network surrounding that channel/account is becoming more and more important,” Oseghale says.
“Security teams that rely solely on platform enforcement will fall behind. Those that invest in continuous exposure management and intelligence-driven monitoring will discover the route of the operation and take down entire attack structures, not just single entities,” he concludes.