Appknox, an enterprise mobile application security solution and its African partner, CED Technologies have made a case for all organizations across verticals to develop Application Programming Interface (API) security strategy.
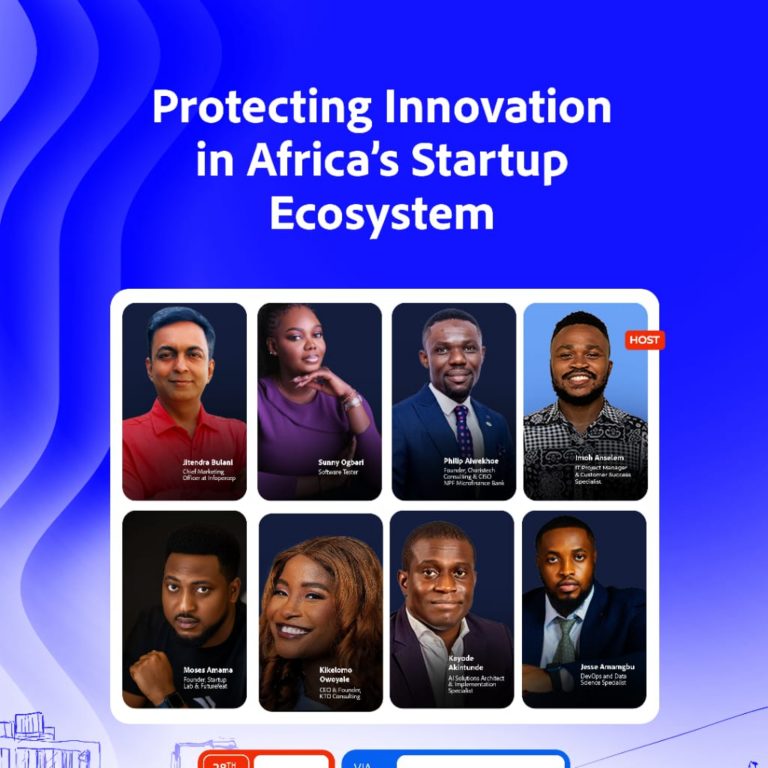
The duo made the case during a webinar with the theme ‘How CISOs Can Build an API Security Program’, which attracted stakeholders such as Head of IT Security, Product Mobile Developers, CISOs, Security Risk Officers and Product Managers.
Speaking on the importance of API security for organizations, Vaidyanath Balasubramanian, Appknox’s Executive Director, explained that API security can help prevent data breaches by ensuring that only authorized users and applications can access the data, and that data is encrypted during transmission.
“Protecting sensitive data is important, but if APIs are not secured, cybercriminals can intercept and steal sensitive information, resulting in significant financial and reputational damage to the organization,” he posited.
Also making inputs, Chukwuebuka Ume-Ezeoke, Chief Technology Officer at CED Technologies, noted that API security ensures that the organization is compliant with regulations such as General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), Nigerian Data Protection Regulation (NDPR), Kenyan Data Protection Regulation (KDPR) and Health Insurance Portability and Accountability Act (HIPAA) by protecting sensitive data and providing secure access to APIs.
Ume-Ezeoke highlighted the risks and consequences of API security breaches including Data Exposure, Business Disruption, Regulatory non-compliance, Reputation damage and cyberattacks.
He added that by developing an API Security Strategy, organisations need to identify API security requirements, choose an API security architecture, implement API security controls, test and validate API security, ensure compliance and continuously monitor and improve.
CISOs always have to balance between enabling and securing the business but achieving that balance has become more difficult in an API-first world where development moves faster than ever before and exposes more sensitive data through an expanding portfolio of APIs – leaving security teams having to play catch-up.
Slides on Developing an API Security Strategy can be obtained via securemyapp@appknox.com or securemyapp@ced.com.ng