Kaspersky has detected a malicious campaign, where attackers leverage AI-generated websites to distribute versions of the legitimate remote access tool Syncro.
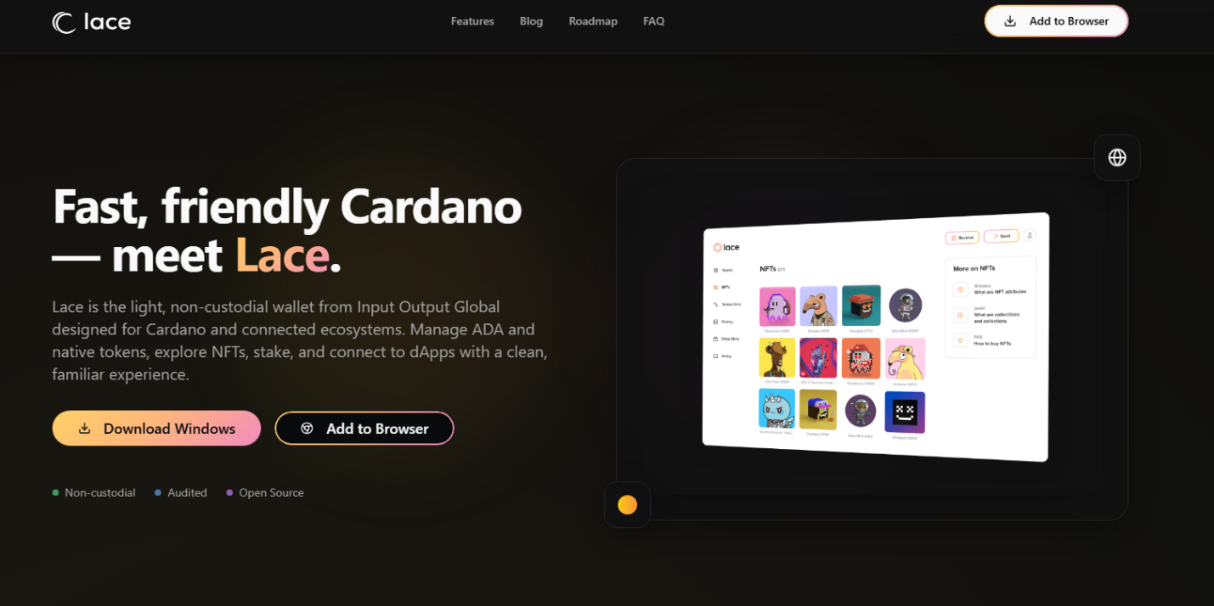
These fake sites attract users via search engines or phishing emails and mimic popular applications like crypto wallets, antiviruses, and password managers, tricking users into downloading legitimate software that is then used for malicious purposes.
The campaign combines scareware tactics, for instance, frightening users with fabricated security alerts – to enable the remote control of victims’ devices, with the goal of stealing crypto.
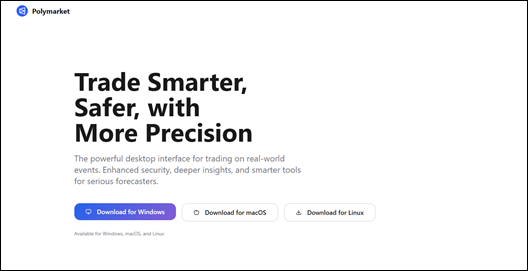
The attackers employ the AI website builder ‘Lovable’ to create professional-looking pages with domains closely matching common search queries on related topics, for instance, Polymarket, a multifunctional prediction market platform.
These sites do not clone originals exactly but create convincing variations, making detection challenging at a glance.
The websites attract traffic through search results or deceptive emails promising token migrations or urging to install a trading app, an antivirus or some software updates.
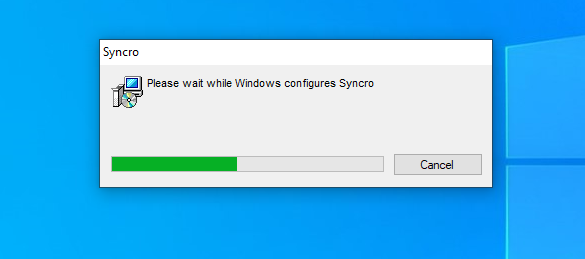
In all cases users end up installing the legitimate Syncro tool, typically used by IT teams for remote management.
For the described attack scenario it comes preconfigured and grants attackers full access to the victim’s devices, including screen viewing, file viewing and command execution capabilities, without triggering standard antivirus flags since it’s not inherently malicious.
“This campaign highlights the evolving threat landscape where legitimate tools are being weaponised through AI-driven deception. By automating the creation of high-quality fake sites, cybercriminals can scale attacks efficiently, preying on users’ trust in familiar brands and urgent warnings. It’s a stark reminder that even signed software from seemingly reputable sources demands scrutiny,” comments Vladimir Gursky, malware analyst at Kaspersky.
To protect against these attacks, Kaspersky recommends avoiding downloads from unverified sources, especially on devices handling finances or cryptocurrencies.
Always verify website URLs against official ones before proceeding, and pay close attention to any remote access tools that are suggested for installation or that are already installed.
Additionally, enable anti-phishing features and conduct regular security audits with solutions such as Kaspersky Premium to mitigate risks from remote access exploits.